If you are interested in social networks, don't miss the slick video about Max Schrems’ David and Goliath struggle with Facebook over the way they are treating his personal information. Click on the red “CC” in the lower right-hand corner to see the English subtitles.
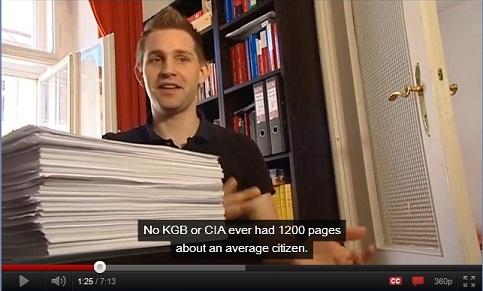
Max is a 24 year old law student from Vienna with a flair for the interview and plenty of smarts about both technology and legal issues. In Europe there is a requirement that entities with data about individuals make it available to them if they request it. That's how Max ended up with a personalized CD from Facebook that he printed out on a stack of paper more than a thousand pages thick (see image below). Analysing it, he came to the conclusion that Facebook is engineered to break many of the requirements of European data protection. He argues that the record Facebook provided him finds them to be in flagrante delicto.
The logical next step was a series of 22 lucid and well-reasoned complaints that he submitted to the Irish Data Protection Commissioner (Facebook states that European users have a relationship with the Irish Facebook subsidiary). This was followed by another perfectly executed move: setting up a web site called Europe versus Facebook that does everything right in terms using web technology to mount a campaign against a commercial enterprise that depends on its public relations to succeed.
Europe versus Facebook, which seems eventually to have become an organization, then opened its own YouTube channel. As part of the documentation, they publicised the procedure Max used to get his personal CD. Somehow this recipe found its way to reddit where it ended up on a couple of top ten lists. So many people applied for their own CDs that Facebook had to send out an email indicating it was unable to comply with the requirement that it provide the information within a 40 day period.
If that seems to be enough, it's not all. As Max studied what had been revealed to him, he noticed that important information was missing and asked for the rest of it. The response ratchets the battle up one more notch:
Dear Mr. Schrems:
We refer to our previous correspondence and in particular your subject access request dated July 11, 2011 (the Request).
To date, we have disclosed all personal data to which you are entitled pursuant to Section 4 of the Irish Data Protection Acts 1988 and 2003 (the Acts).
Please note that certain categories of personal data are exempted from subject access requests.
Pursuant to Section 4(9) of the Acts, personal data which is impossible to furnish or which can only be furnished after disproportionate effort is exempt from the scope of a subject access request. We have not furnished personal data which cannot be extracted from our platform in the absence of is proportionate effort.Section 4(12) of the Acts carves out an exception to subject access requests where the disclosures in response would adversely affect trade secrets or intellectual property. We have not provided any information to you which is a trade secret or intellectual property of Facebook Ireland Limited or its licensors.
Please be aware that we have complied with your subject access request, and that we are not required to comply with any future similar requests, unless, in our opinion, a reasonable period of time has elapsed.
Thanks for contacting Facebook,
Facebook User Operations Data Access Request Team
What a spotlight
This throws intense light on some amazingly important issues.
For example, as I wrote here (and Max describes here), Facebook's “Like” button collects information every time an Internet user views a page containing the button, and a Facebook cookie associates that page with all the other pages with “Like” buttons visited by the user in the last 3 months.
If you use Facebook, records of all these visits are linked, through cookies, to your Facebook profile – even if you never click the “like” button. These long lists of pages visited, tied in Facebook's systems to your “Real Name identity”, were not included on Max's CD.
Is Facebook prepared to argue that it need not reveal this stored information about your personal data because doing so would adversely affect its “intellectual property”?
It will be absolutely amazing to watch how this issue plays out, and see just what someone with Max's media talent is able to do with the answers once they become public.
The result may well impact the whole industry for a long time to come.
Meanwhile, students of these matters would do well to look at Max's many complaints:
|