Eric Schultz writes with this question:
I've been investigating CardSpace and the practicality of it's use for login on a new social networking site.
I have a question regarding the method through which data is transferred. I see that you can require certain claims from an InfoCard such as email, first and last name, zip code etc. When I look at the login code I see that the same claims are required again.
Does this mean that each time an InfoCard is sent all the personal data is resent? Isn't this dangerous for security/privacy? The potential for a server failure (malicious or not) caused by a buffer overflow, a coding mistake that outputs the details of session variables etc. seems rather risky in this scenario.
Perhaps I am being alarmist?
This is an area in which being “an alarmist” – perhaps I will rephrase it as being thoroughly pessimistic about what can go wrong – is the best starting point. You questions are ones everyone should think about.
InfoCard and Minimal Disclosure
The simple answer is that there is nothing built into InfoCard concepts that requires a “relying party” to ask for attributes every time a user comes to its site. Let's first look at the mechanics.
The relying party controls what attributes it asks for by putting an OBJECT tag in the HTML page where the user opts to use an infocard.
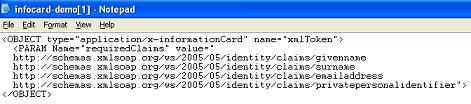
The example shown here will bring up the infocard dialog and illuminate any cards that offer all four claims so the user can select one.
If, next time, the relying party doesn't want to receive these claims, it just doesn't ask for them. If it has stored them, it should be able to retrieve them when necessary by using “privatepersonalidentifier” as a handle. This identifier is just a random pairwise number meaningless to any other site, and so there is no identity risk in using it.
No theoretical bias
In other words, the InfoCard system has no theoretical bias about what information should be asked for when. Through the Laws of Identity we have tried to help people understand that they should only ask for what they need to complete a transaction and should only keep it for the length of time they absolutely must.
In particular, there should be no hoarding of rainy-day information – information that “might come in handy” some day – but which is more likely to turn into a liability than into a benefit.
Do your risk analysis
You'll need to do the conventional risk analysis and think about whether it is more dangerous to store the information or just ask for it on an “as-needed” basis and then forget it. My personal sense is that it is more dangerous to store it than to use an on-demand approach.
A central machine with the stored information that animates a successful internet business is a honeypot. It could well be subject to insider attacks, and certainly, since it lives on the internet, will be subject to many attacks on the information it stores. Why not avoid these problems completely?
Certainly, the on-demand approach has benefits in convincing customers and legal practitioners that, having held no identity information, you cannot be seen as being responsible for an identity meltdown. To me this is very attractive, and something that has not been possible until now.
Conclusion
The examples Eric gives of things that can go wrong seem to me to apply even more strongly if you have stored information locally than if you ask for it on demand.
But as I said earlier, this just expresses my thinking – there is lots more to be written by Eric and hundreds of others as they develop applications.
Meanwhile, InfoCard has no built-in assumptions around this and can be used in whatever way is appropriate to a given situation.

Would it be fair to say that the site might have two separate requests for an InfoCard?
1) Frequest log-in: this would just have the site-specific token
2) Form fill-out bucket: A “request information” InfoCard that would ask (as optional) all relavant fields that a user may choose to display on the social networking site.