[This is the fourth installment of a presentation I gave to Microsoft developers at the Professional Developers Conference (PDC 2008) in Los Angeles. It starts here.]
 We have another announcement that really drives home the flexibility of claims.
We have another announcement that really drives home the flexibility of claims.
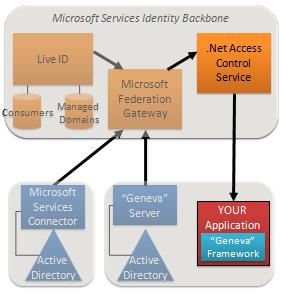
Today we are announcing a Community Technical Preview (CTP) of the .Net Access Control Service, an STS that issues claims for access control. I think this is especially cool work since it moves clearly into the next generation of claims, going way beyond authentication. In fact it is a claims transformer, where one kind of claim is turned into another.
An application that uses “Geneva” can use ACS to externalize access control logic, and manage access control rules at the access control service. You just configure it to employ ACS as a claims provider, and configure ACS to generate authorization claims derived from the claims that are presented to it.
The application can federate directly to ACS to do this, or it can federate with a “Geneva” Server which is federated with ACS.
ACS federates with the Microsoft Federation Gateway, so it can also be used with any customer who is already federated with the Gateway.
The .Net Access Control Service was built using the “Geneva” Framework. Besides being useful as a service within Azure, it is a great example of the kind of service any other application developer could create using the Geneva Framework.
You might wonder – is there a version of ACS I can run on-premises? Not today, but these capabilities will be delivered in the future through “Geneva”.
Putting it all together
Let me summarize our discussion so far, and then conjure up Vittorio Bertocci, who will present a demo of many of these components working together.
- The claims-based model is a unified model for identity that puts users firmly in control of their identities.
- The model consists of a few basic building blocks can be put together to handle virtually any identity scenario.
- Best of all, the whole approach is based on standards and works across platforms and vendors.
Let’s return to why this is useful, and to my friend Joe. Developers no longer have to spend resources trying to handle all the demands their customers will make of them with respect to identity in the face of evolving technology. They no longer have to worry about where things are running. They will get colossal reach involving both hundreds of millions of consumers and corporate customers, and have complete control over what they want to use and what they don’t.
Click on this link – then skip ahead about 31 Minutes – and my friend Vittorio will take you on a whirlwind tour showing all the flexibility you get by giving up complexity and programming to a simple, unified identity model putting control in the hands of its users. Vitorrio will also be blogging in depth about the demo over the next little while. [If your media player doesn't accept WMV but understands MP4, try this link.]
In the next (and thankfully final!) installment of this series, I'll talk about the need for flexibility and granulartiy when it comes to trust, and a matter very important to many of us – support for OpenID.