I've heard many positive comments about Pam Dingle's talk on “InfoCard in the Enterprise” at the Directory Experts Conference in Vegas. Unfortunately I couldn't get to Vegas – but here's her recent post.
Things went along just swimmingly last night at my “Infocard in an Enterprise Context†talk at the Directory Experts Conference. There were many insightful questions from the audience, and afterwards, it warmed my geeky little heart to see Stuart Kwan surrounded by crowds of administrators, all wanting to give feedback and have questions answered.
There were some very interesting topics brought up during the discussion, which I want to capture before I forget. The most discussed topics surrounded that of “card proliferationâ€. If you end up having as many different managed cards on your desktop as you do cards in your physical wallet, does that become easier or harder to use than regular username/password combinations?
It is a really good point. A great example was brought up, which was identification cards for gambling establishments. What if you have 20 membership cards for 20 casinos? There are two ways that those casinos might want to do the infocard thing: either they could give you a managed card with that information in it, or they could register your self-asserted card.
In the first case, you literally would end up with 20 different cards. Remember though, in that case the gambling establishment would be requiring an exact issuer, so ALL the cards in your wallet would be greyed out except the right one, and that the same card would always be used for transactions with that site, so it would always pop up at the top, with the “you used this card last time, would you like to use it again? messageâ€. In the second case, you could create a “gambling card†that could be registered at as many sites as you wished. You could do this safely, because nothing in the information stored in the infocard is specific to any one of the gambling institutions, it is just personal contact information. Instead of you giving them your membership number, you are giving them your PPID, which is associated with your membership number at the gambling site. By doing so, you have completely removed any data from the card that would be of interest to steal, or that could be accidentally given away during the process of using the card at multiple sites. Remember that a PPI is a calculated identifier that is different for every Relying Party.
I think that at least in the beginning, that 2nd case will be more common. However, users themselves will not be able to choose what kind of card the Relying Party demands, and besides, the root point of the original question remains. How many cards do YOU have in your wallet? How many username/password combos have you, over the years, accumulated? If Infocard really takes off, there is no doubt that people will begin to accumulate infocards, even if they work hard to keep their cardsets small.
I can’t speak for MS of course, but I’m pretty sure that the Infocard team would be delighted to have this technology become so popular that they have to race to get rid of the currently existing card limit (I know there is one, can’t remember what it is) and implement mass-management tools for the interface sooner rather than later (-:
Another discussed topic was the idea of having cards that had some controlled fields and some open fields. That one is a topic for a whole other conversation, and a very interesting concept.
Lastly – Dave Kearns asked me what about my presentation was “user-centricâ€. I replied “nothing†as I was specifically addressing how the identity metasystem could be locked down and controlled/audited/managed centrally to satisfy business needs. I think that perhaps that answer was flippant — users still get to see what of their information is being passed in the enterprise, and they can also choose which corporate credentials they wish to use for what corporate resources — this is still an increase in choice and visbility to what they have now.
If you were there and if you are interested in trying this technology out, here is a uber-quick set of instructions and gotchas:
- Although infocard will run on both W2K3 and XP sp2, I suggest using XP sp2, as IE7 beta previews are not yet supported on W2K3
- Getting the right version of IE7 is *critical*. I don’t know all the version numbers, but the version I have works – IE7 Beta preview 2. There was another version following that which does NOT work, so be careful. If you can’t afford the time to be wrong, let me know and I’ll make sure you get a working version.
- Don’t use a host system that you have any attachment to. If you want to follow the CTPs as they come out, you will almost certainly have to start from scratch (for example, moving from the Jan CTP to the Feb CTP required a vanilla install). Use VMs if you can.
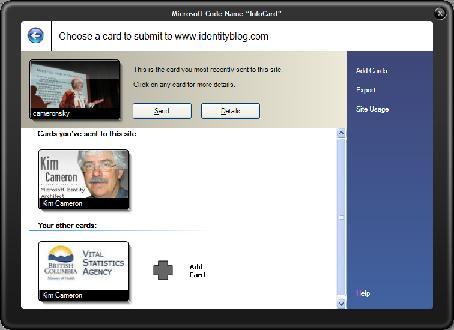
- Apparently (and I haven’t even tried it yet, it is that new), there are now TWO Relying Parties on the internet that you can go to with your new Infocard client, Kim Cameron’s Identity Blog and Chuck Mortimore’s Java-based Relying Party.
Thanks again to everyone who attended, I hope that y’all had fun.
Update: Jef comments that IE7 version 5335 fails, and that he got version 5299 to work. I also know that Rohan Pinto had trouble with version 5299 and had to resort to 5296. No matter what, it seems that 5335 is a no go, so I hope that helps! Thanks Jef.
At this point, I think the best thing to do is get the MIX06 bits if you want to experiment with the InfoCard sites. I'm definitely publishing my PHP sample code and tutorials this week, so stay tuned.

 Providing identity services between people, websites, and organizations that don't necessarily have a formalized relationship is a different problem than providing authentication and authorization services within a single organization.
Providing identity services between people, websites, and organizations that don't necessarily have a formalized relationship is a different problem than providing authentication and authorization services within a single organization. and energizing that we will be using this format for both days. If you have a presentation that you would like to make or a topic that you know needs discussion in the community you can propose it here on the wiki. We will make the schedule when we are face to face at 9AM on May 2nd. We do this in part because the ‘field’ is moving so rapidly that we your organizing team are in no position to ‘know’ what needs to be talked about. We do know great people who will be there and it is the attendees who have a passion to learn and contribute to the event that will make it.
and energizing that we will be using this format for both days. If you have a presentation that you would like to make or a topic that you know needs discussion in the community you can propose it here on the wiki. We will make the schedule when we are face to face at 9AM on May 2nd. We do this in part because the ‘field’ is moving so rapidly that we your organizing team are in no position to ‘know’ what needs to be talked about. We do know great people who will be there and it is the attendees who have a passion to learn and contribute to the event that will make it.