Scotland's eCare has been recognised at an international awards ceremony on good practice in data protection. On Tuesday, 11 December, the Data Protection Agency of the Region of Madrid awarded the eCare framework one of two “special mention” awards. The aim of the annual prize is to expand the awareness of best practices in data protection by government bodies across Europe.
I'm really pleased to see the authors of eCare recognized. They have created a system for sharing health information that concretely embodies the kind of thinking set out in the Laws of Identity.
A Scottish Executive publication describes eCare this way:
The system is designed with a central multi-agency eCare store in a ‘demilitarised’ zone (hanging off NHS net), which links to the multiple back office legacy systems operating locally in the partner agencies. This means that each locality will have its own locally defined and unique approach.
All data shared is subject to consent by the client. The system users are authenticated through their local systems, and are only entitled to view the data of their clients. Clients can change their consent status, and as soon as this is logged on the local system the records cannot be viewed by the partner practitioners.
Benefits that the programme will deliver
The direct benefit to the citizen will be through improved experience of care. Single Shared Assessment, through electronic information sharing, will reduce the volume of questions repeatedly asked by professionals, as data will only have to be collected from the client once, then shared through the technology.
The Children's Services stream will focus on the delivery of an electronic Personal Care Record, an Integrated Children’s Services Record, and a Single Assessment Framework for sharing, to benefit both Scotland’s children, and care practitioners. Across the streams’ care groups, practitioners will save time, because core data will be shared, rather than gathered by multiple agencies. This will reduce the possibility of duplicated or inappropriate care. A more holistic picture of the client will be created, which will help to ensure services that more accurately meet peoples needs.
The principal deliverables of the Learning Disability stream are the development of integrated local service records, which will help planning across a range of services, and the piloting of a national anonymised database, which will enable the Scottish Executive to monitor implementation of ‘The same as you?’ initiative.
Ken Macdonald, Assistant Commissioner (Information Commissioner’s Office, which provided a note of support for the eCare application) has commented:
It is wonderful to see UK expertise in data protection being officially recognised in Europe for the second year running. Recent events have highlighted the need to comply with the principles of the Data Protection Act and I am delighted to see the eCare Framework and the Scottish Government setting such a fine example to others not just in the UK but throughout Europe.
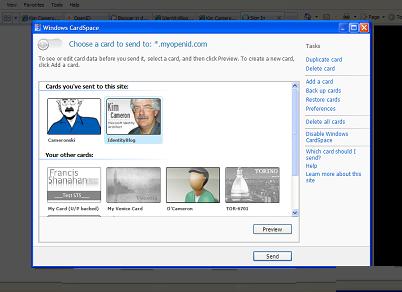
I hope the work is published more broadly. From seeing presentations on the system, it partitions information for safety. It employs encrypted data, not simply network encryption. It favors local administration, and leaves information control close to those responsible for it. It puts information sharing under the control of the data subjects. It consistently enforces “need to know” as well as user consent prior to information release. In fact it strikes me as being everything you would expect from a system built after wide consultation with citizens and thought leaders – as happened in this case. And not surprisingly with such a quality project, it uses innovative new technologies and approaches to achieve its goals.