Greg Mulholland, a British MP, has drawn my attention to a misuse of identity technology that not only concerns me, but saddens me.
I'm a pretty hard-bitten technologist. I long ago observed that one of the unfortunate characteristics of computers is that they allow people to do stupid things thousands of times more quickly than they did before.
But this one goes beyond silly to abusive. It involves inflicting a technology that is not yet ready for use in the real world, on young children. An analogy might be a decision, by people who don't realize testing is necessary, to inject students with an untested vaccine. And worse, the parents have no opportunity to opt out.
This is one of those cases where ignorance breeds Sorcerer's Apprentices who act without the slightest knowledge that there will be consequences to what they do.
On a personal note, I can't help responding as one who has taught – albeit, not to children. I wonder what has happened to our teachers, whose job must be to know their students intimately and respond, with open hearts, to their needs and abilities? What macabre pathways led them to introduce impersonal and mechanized technologies like RFID and – the mind boggles – fingerprinting, as a substitute for personal interaction? I see a tear in Socrates’ eye.
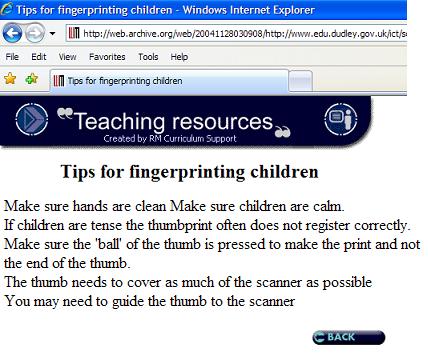
In Britain, not only do an estimated 3,500 schools already use fingerprinting, but, in astonishing ignorance of the first law of identity, parental consent is not required. If it had been, the technical and security issues now coming to light would have been raised earlier, and the money which has been poured down this pathetic technology drain could have been used to better ends.
The following is a story on the BBC web site about the growing controversy and the government's new “guidelines” on fingerprinting in schools:
The guidelines, published next month, will “encourage” schools to seek consent before taking biometric data.
The move comes after it emerged some primary schools stored children's thumb prints for computerised class registers and libraries without parental consent.
The Department for Education and Skills (DfeS) says it does not have figures for how many schools are already using biometric data.
However, a web poll by lobby group Leave Them Kids Alone, estimated that 3,500 schools had bought equipment from two DfES-approved suppliers.
Under the Data Protection Act, schools do not have to seek parental consent to take and store children's fingerprints.
‘Sensitive area’
But privacy watchdog the Information Commissioner will urge them to do so from next month after pressure from parents and campaign groups.
“Because this is a fairly sensitive area – because young people are going to be sharing their personal information – we are encouraging schools to adopt best practice and seek the consent of both pupil and parent,” a spokesman for the Information Commissioner said.
Schools will also be reminded that they must not share the data with other organisations.
They have also been told they should only hold fingerprint and other information “as long as it necessary for the purpose for which it is being processed”.
But the moves are unlikely to satisfy campaigners, who have been calling for a change in the law to ban fingerprint scanners from school premises.
‘Social conditioning’
The director of lobby group Action on Rights for Children, Terri Dowty, said having fingerprint technology in schools – allowing students to register, use the library and buy canteen food – was “encouraging children to be casual about their biometric data”.
Her views were echoed by Phil Booth from the anti-identity card campaign group No2ID.
He said: “We're talking about social conditioning. In a school environment it will make kids less concerned about their biometric data.”
But he also raised concerns about storing such information on “relatively insecure databases”.
Parent activist David Clouter said a lack of guidance from the DfES and the Information Commissioner had “produced a juggernaut of companies wanting to jump on the bandwagon” to sell equipment to schools.
‘Stolen identities’
He had been told that having biometric data in school libraries “would encourage people to read”.
“Given that children have been reading for centuries I find that hard to believe”.
A technology expert, Andrew Clymer, who has campaigned to keep biometrics out of the school attended by his children, aged six and eight, said that no IT system was guaranteed to last beyond a few years.
However, a fingerprint taken from a 4-year-old child would last a lifetime.
“Security is always developed with a timeframe, but biometric data is for a lifetime.
“We would potentially be opening up the possibility that in the future kids will have their identities stolen,” Mr Clymer said.
Guidance
Forty-seven MPs have signed a Commons motion tabled by Liberal Democrat MP Greg Mullholland calling for consent to be required for the collection of biometric data.
Shadow schools minister Nick Gibb has also asked schools minister Jim Knight about guidance.
Mr Knight responded that biometric information about pupils should be handled in the same way as other personal data about pupils, and said it was subject to the Data Protection Act 1998.
Under the Act, schools are not obliged to seek consent from parents, but they should provide notification of their use of data to individuals involved.
‘Common sense’
The DfeS said fingerprints were used to help make school libraries, lunches and “management systems” run more smoothly and the information was stored as a “digital number stream” rather than individual prints.
Schools are also required by the Data Protection Act to tell parents about any information being held on their children and what it is being is used for.
A DfeS spokesman said: “It is important to remember that schools have always collected personal information, such as registers and home addresses, on pupils for their own smooth running.
“They are well used to handling all kinds of sensitive information to comply with data protection and confidentiality laws.
“Parents should be engaged in all aspects of school life and it is common sense for schools to talk to them about this and all issues relating to their children.”
The new guidance for schools will be available from the end of March on the website of Becta, the British Educational and Communications Technology Agency.

 Received this email from a reader. Has anyone any idea what was going on?
Received this email from a reader. Has anyone any idea what was going on?