Bandit's contribution to the emerging identity metasystem is exceptional – we're talking about the DigitalMe Identity Selector for Mac and Linux , as well as relying party components. I will post a download link as soon as one becomes available. Novell's Dale Olds wrote about the Catalyst Conference and OSIS Interopathon here : Continue reading DigitalMe for Mac passed the Interoperathon
Category: Higgins
Catalyst Interopathon reveals sea change
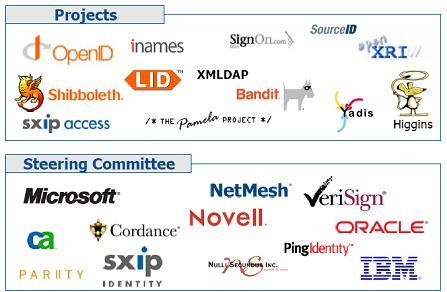
Here are the logos of the projects participating in the Information Card Interopathon at the Burton Group's Catalyst Conference. Beyond that, people told me about at least half a dozen new open source projects (each with a unique mission) that are sitting in the wings getting ready to go public. I'll try to keep you posted on these.
We had a rehearsal for this a couple of months ago at Internet Identity Workshop, but something has changed since then: many of the players seem to have made strides in getting concrete about how the technology would be used in their products. That's the key.
According to the press release:
Participants include projects groups Eclipse Higgins Project, Internet2 Shibboleth Project, The Pamela Project, Ian Brown (OpenInfoCard), XMLDAP, and SocialPhysics and vendors BMC Software, CA, FuGen Solutions, IBM, Microsoft, NetMesh, Novell, Nulli Secundus, Oracle, Ping Identity, Sxip Identity, VeriSign, and WSO2.
The demonstration will be centered on a photo sharing application and will show the breadth and maturity of user-centric technologies by executing a variety of information card-based component capabilities including:
- Protocol and wire format interoperability
- Card format interoperability
- Policy interoperability
- Platform interoperability
The interop event was organized by OSIS and identity commons and hosted by The Burton Group. Thanks to all involved.
Neil Macehiter on the identity metasystem
Here is some recent commentary from Neil Macehiter at macehiterward-dutton Blog on IT Business Alignment:
It's perhaps unsurprising, given all the brouhaha surrounding Microsoft's claims that open source software infringes on 235 of its patents (which incidentally I take to be largely ‘sabre rattling’ from Redmond in the face of the implications of the GPLv3 for its deal with Novell, as discussed in the Risk Factors of the latter's recent 10-K filing), that some recent news regarding the Redmond company's very positive collaboration with the open source community has not received the attention it deserves.
The news in question concerns a series of announcements the company made at last week's Interop conference in Las Vegas. These announcements, as the title of the post suggest, all revolve around Microsoft's vision for an Internet-scale, interoperable identity metasystem and range from additions to the Open Specification Promise (OSP) through to support for OpenLDAP with Microsoft's Identity Lifecycle Manager.
So, what did they announce? First, Microsoft is
making the Identity Selector Interoperability Profile available under the OSP to enhance interoperability in the identity metasystem for client computers using any platform. An individual open source software developer or a commercial software developer can build its identity selector software and pay no licensing fees to Microsoft, nor will it need to worry about future patent concerns related to the covered specifications for that technology
In other words, third parties are free to build the equivalent of Microsoft's CardSpace, following the likes of the Higgins project, Ian Brown's Apple Safari Plug-In and Chuck Mortimore's Firefox Identity Selector. This is important not only because it extends the reach of CardSpace-like capabilities beyond Windows but also because it facilitates the consistent user experience (I know because I have used CardSpace, the Safari Plug-In and the Firefox Identity Selector) which helps to reduce errors and misunderstanding by users.
Second, Microsoft
is starting four open source projects that will help Web developers support information cards, the primary mechanism for representing user identities in the identity metasystem. These projects will implement software for specifying the Web site’s security policy and accepting information cards in Java for Sun Java System Web Servers or Apache Tomcat or IBM’s WebSphere Application Server, Ruby on Rails, and PHP for the Apache Web server. An additional project will implement a C Library that may be used generically for any Web site or service. These implementations will complement the existing ability to support information cards on the Microsoft® Windows® platform using the Microsoft Visual Studio® development environment.
Or, to put it another way, doing for back end servers what the first announcement is doing for the front-end: enabling web sites and enterprises running a wide variety of web server infrastructure to support authentication using CardSpace and the other identity selectors.
The cyncical amongst you might be forgiven for thinking that these two announcements are just Microsoft paying lip service to interoperability. This post should help to allay your concerns: at the Internet Identity Workshop earlier in May the Open Source Identity Selector (OSIS) group demonstrated interoperability amongst 5 identity selectors, 11 relying parties (the party relying on authentication to prove an identity), 7 identity providers (the party asserting the identity), 4 types of identity token (the mechanism for conveying the identity assertion), and 2 authentication mechanisms. Also, on the same day as the Microsoft press release, Internet2 announced plans to extend Shibboleth, a federated web single sign-on solution based on SAML that is widely used amongst educational institutions, to support CardSpace and compatible identity selectors.
The third piece of news from Redmond last week, concerned the new Identity Lifecycle Manager product and is thus primarily focussed behind the firewall. Microsoft is going to be working with KERNEL Networks and Oxford Computer Group to enable bi-directional synchronisation of identity data between OpenLDAP, an open source implementation of the ubiquitous directory standard, and Microsoft's Active Directory. Identity Lifecycle Manager already supports a wide range of the commonly-deployed identity data repositories so I think this move is primarily in the “playing well with open source” category – but valuable nonetheless.
These announcements are further evidence that the likes of Kim Cameron, Microsoft's chief identity architect, and Mike Jones, the company's Director of Identity Partnerships, have been working hard to foster the relationships and commitment (both from Microsoft and third parties) required to help make the identity metasystem a reality. That reality is too important for the results of those efforts to be diluted by political shenanigans around patents and GPLv3.
I'm glad to hear that Neil has tried CardSpace and its sister implementations on different platforms.
Nick Shelness on CardSpace
The strangest thing just happened. I was following a link that had just appeared from vowe.net – a site published by Volker Webe. An interesting site, for sure – and on it, I read this piece by Nick Shelness:
Establishing identity and authenticating on the web are a mess. I doubt I’m alone in using the same user id and password over and over again. If they’re hacked once they can be employed a hundred times over. Yeah, some sites make you change your password at regular intervals, but how do you remember them? I write them down, and carry them with me. OK, they’re somewhat encoded, but …
For some time now, there has been the possibility of improvement under the “Identity 2.0†banner. To the surprise of some (many?), a significant chunk of Identity 2.0 innovation has come from Microsoft, and no, no, no, it’s not “Passportâ€. It is expressed in two seminal papers: The Laws of Identity and The Identity Metasystem, both by Kim Cameron.
But this is not all. There is a Microsoft product. It’s called “CardSpace†(it used to be called “Info Cardâ€). It ships as part of Vista. It also ships as an automatic XP upgrade, and there are a host of alternatives, including open source ones.
CardSpace and its analogues, on their own, are not a solution. They are a component, albeit a key one, of an Identity Metasystem. What needs to come next is for web sites (“Relying Partiesâ€) to start requesting and employing CardSpace-managed security assertions. This in turn will create a demand for Identity Provision (yes, this is where ActiveDirectory and son of Passport come in).
Will this happen? It’s too early to say. But by seeding the digital world with CardSpace, Kim and Microsoft have taken us a long first step down this path, and IMHO done us all a big favor.
It took me a minute to click in to the name Nick Shelness. He is a great visionary – CTO at Lotus and later an IBM fellow (now with his own practice in the UK). His support means a lot to me.
As for his “will it happen?” question, I've asked it too on a hundred ‘bleak and dreary days’. But I continue to think there are historical inevitabilities at work here.
Distributed computing is dammed up behind a wall of identity friction. The one good thing about the friction is that it limits phishing and cyber crime as much as it limits business. Remove the friction with something like single sign-on and you massively increase the attraction of the digital honeypot, providing a one-stop attack surface for evil. The more consolidated identity initiatives succeed, the more they will fail – unless there is a paradigm change like CardSpace that compensates for risk aggregation.
Few may understand these dynamics through theory alone, but Professor Reality will come to tutor them before too long. Meanwhile, there are more and more people with enough vision that they don't have to “go over Niagra Falls in a barrel to know it hurts.”
Day after day, week after week, month after month, CardSpace “sockets” are appearing on desktops. One day – not too far into the future – it will be present on 50% of them. Then on 75%! Meanwhile the software will get slicker and slicker, with multiple versions and choices by people like our friends at Higgins running on Mac and Linux. This is a historic thing we are doing together, and we can't be impatient. But this baby is going to light up big time.
Jeff Bohren on role of CardSpace
Jeff Bohren at BMC Software has an interesting take on CardSpace and TEG – as well as other related matters. And in this posting he says that BMC Software will be participating in the interoperability event at the next Burton Catalyst. This really adds to the momentum.
There will be a User Centric interoperability event at the next Burton Catalyst in SF. This will bring together several IdM vendors and open source projects to demonstrate interoperability between different implementations of Cardspace/InfoCard and OpenID. BMC Software will be participating. We will also have a hospitality suite the following night. I will be there so if you want to drop by I would be glad to talk with you about IdM issues.
Mike Jones from Microsoft has some great Cardspace/InfoCard resources on his blog. If you are interested in this area, you should definitely check this out. You should also check out Pamela Dingle’s introduction to Cardspace.
Microsoft has recently announced that they have sold over 40 million copies of Vista in the first 100 days since its release. Obviously not all of those are installed and in use, but this still a lot of users. And every one of them is a potential Cardspace user.
If IE isn’t your cup of tea, there are several other option available. Xmldap.org has a plug-in for Firefox. I gave it a try, but for some reason I could not use it to do InfoCard authentication to Kim Cameron’s blog, which you can obviously do with CardSpace.
There has been a recent spurt of debate over at the TEG mailing list about Cardspace. I don’t want to waste TEG bandwidth on what is really a tangential issue, so here is my take on the value of Cardspace/InfoCard.
The best way to think of the value of Self-Issued InfoCards is to think of them as analogous in feature to end-user SSL client certificates. In essence they are a holder-of-key style authentication that can be used by itself or in conjunction with a password based authentication to dramatically improve the security of the authentication process. Like client certificates, InfoCards authenticate the computer the user is on, not the user. They further have the advantage of presenting a very user friendly graphical mechanism to select what identity should be used.
While all InfoCard implementations have this value, Cardspace goes further and adds additional features to thwart phishing, man-in-the-middle-attacks, and software key loggers. If the US banks where smart, they would adopt InfoCard as their solution to comply with FFIEC guidance for on-line banking. Cardspace/InfoCard could be used as a second factor of authentication to use for financially sensitive transactions. Not as a replacement for passwords, but as a supplement. And best of all (to the bank) there is zero cost on a per user basis.
For enterprises there is an important potential value for InfoCards, and it has nothing to do with internal authentication. The value is by using InfoCards, an employee of a company can easily choose different identities depending on whether he is representing the company in a specific transaction or not. It has to do with separating personal from professional personas. A company could issue a managed InfoCard to each employee for use for their professional persona and establish best practices for using their self-issued InfoCards for personal business. Now you can do this without InfoCards by creating multiple IDs, but as a practice no one does that.
Update 5-24-07
Shibboleth just announced that they will add support for Cardspace/Infocard in the Shibboleth architecture. Kim Cameron's thoughts about it are here and Mike Jone's comments are here. This is a great development. The Shibboleth project has a great deal of respect and mind share in the identity community.
I'm not sure I agree that InfoCards authenticate the computer the user is on, and not the user. I think that depends on whether they are combined with a challenge such as a one-time password. I hope Jeff writes more about what he means by this.
6 year old installs keylogger
Here is a strange one via Pamela Dingle's eternal optimist:
How girl, 6, hacked into MP’s Commons computer
I assume a physical keyboard logger like this could still be used to steal an IdP username & password, even with all the secure desktop stuff that the CardSpace client has built in…
This kind of dongle plugs in between the keyboard and the computer. So there is one simple solution: don't type in secrets that could allow someone to gain access to your accounts.
My view:
- CardSpace self-issued cards ( based on public key technology) and managed cards backed by a self-issued card or certificate would both be immune to this attack – assuming no physical access to the computer itself.
- Normal Kerberos login would be vulnerable.
- Username / password IdP's could be protected from this attack through use of the additional per-card secret described here – assuming non-InfoCard password access was not supported.
- One time password (OTP) systems would be unaffected.
BTW, I now have OTP integrated with my own managed card demo code. When used with CardSpace it has very nice security properties because the channel from CardSpace to the IdP is encrypted using information in the managed card and the password can never be reused.
Mike Jones and self-issued.info
Everyone who has met me has probably met my colleague Mike Jones, who put his work as a researcher at MSR on hold because he got so interested in user-centric identity and Information Cards. He has now started to blog – check out the InfoCard showing Mike and Dale onstage at Novell Brainshare.
For those new to Information Cards, you don't normally share an InfoCard with someone else. This was truly a “they did it because they could” moment…
On March 21st at Novell’s BrainShare 2007 conference, Dale Olds and I co-presented the session “Who are you? From Directories and Identity Silos to Ubiquitous User-Centric Identityâ€. Our presentation was a brief history of digital identity solutions, ranging from a password per application to interoperable user-centric digital identity using the Information Card metaphor and several steps in between.
The coolest thing in the session was the first public demo of the Bandit/Higgins cross-platform Identity Selector. During the demo Dale and I both used the same self-issued Information Card (that I created on the BrainShare show floor 🙂 ) to log into a Bandit relying party site, Dale from Linux and me with Windows CardSpace. As Dale and Pat Felsted blogged, two days later the Bandits also demonstrated their selector running on the Mac. Also see Pat’s post on the Details of the Cross Platform Identity Selector.
Great progress towards enabling everyone to answer the question “Who are you?†online with the Information Card of their choice!
BTW, you'll see that Mike, like me, is using pamelaware for WordPress – and accepts comments through infocards. If you use WordPress, you should check it out.
Bandits strike at BrainShare
Incredible news from Dale Olds’ VirtualSoul at Novell:
This week was Novell’s Brainshare conference. It’s a big deal for Novell folks and it’s a great event. It gives us a place to show off new technologies like the emerging Internet identity systems and some of the recent work that we have done on the Bandit team.
Our most significant demo this year was shown during the technology preview keynote on Friday. The whole series of demos is interesting — I especially liked some of the Linux desktop stuff — but if you want to just skip to the infocard stuff, it starts at about 40 minutes into the video.
For those who may want to know more detailed information about what the demo actually does, let me give some background information here:
There were 3 new open source components written by Bandits and made available this week:
- A fully open source, cross platform identity selector service was contributed to Higgins. Written in C++, this Higgins ISS runs as a daemon (no UI) and provides core infocard selector service: it accesses multiple card stores, enumerates available cards, matches cards based on requested claims, and interacts with the appropriate STS to get a token. It is almost complete on support for personal cards, with an internal STS, etc. The real deal.
- A UI process for the Higgins ISS. It is currently written in C#, runs on Mono, and leverages much of the management UI of the CASA component of Bandit.
- A new OpenID context provider was contributed to Higgins. This context provider plugs into the Higgins IdAS and allows identity data to be accessed from any OpenID Provider. What this means is that, with no change to the Higgins STS code (since the STS uses IdAS), we could set up a demo such that infocards can be generated from any OpenID identity. In other words, using the Higgins STS and the new OpenID context provider, I can access any site that accepts infocards with my openID account.
So what Baber showed in the demo:
- A fully functional, native infocard selector running on the Mac.
- He accessed a shopping site with an infocard generated from an OpenID account. Put some things in the cart and logged out.
- Baber switched to a SUSE Linux Desktop machine. Fully functional infocard selector there as well. Accessed the same site with an OpenID infocard and see stuff in his cart from the Mac session.
- Goes to check out. The site asks for a card with different claims, needs a payment card.
- The Higgins Infocard selector supports multiple card stores. In this case Baber selects a credit card from a card store on his mobile phone via bluetooth.
- He authorizes a (hypothetical) payment and the online shopping site (the relying party) only gets his shipping address and an authorization code from the credit card.
It’s a simple demo, and easy to miss the number of technologies and interactions involved, but this is the kind progress that we have been working towards for a long time.
The Bandits are happy and tired.
Bandit and Higgins hit interop milestone
I was so snowed under trying to work against time for the OpenID annoucement at RSA that I missed blogging another imporant milestone that has been reached by the identity community. This report on progress in the Higgins and Bandit side of the house is great news for everyone:
The Bandit and Eclipse Higgins Projects today announced the achievement of a key milestone in the development of open source identity services. Based on working code from the two projects and the larger community of open source developers, the teams have created a reference application that showcases open source identity services that are interoperable with Microsoft’s Windows* CardSpace* identity management system and enable Liberty Alliance-based identity federation via Novell® Access Manager. This reference application is a first-of-its-kind open source identity system that features interoperability with leading platforms and protocols. This ground-breaking work will be demonstrated at the upcoming RSA Conference in San Francisco.
“There are two basic requirements for translating the potential of recent identity infrastructure developments into real-world benefits for users: interoperability and a consistent means of developing identity-aware applications,” said Jamie Lewis, CEO and research chair of Burton Group. “First, vendors must deliver on their promise to enable interoperability between different identity systems serving different needs. Second, developers need a consistent means of creating applications that leverage identity while masking many of the underlying differences in those systems from the programmer. The Bandit and Eclipse Higgins interoperability demonstration shows progress on the path toward these goals. And the fact that they are open source software projects increases the potential that the identity infrastructure will emerge as a common, open system for the Internet.”
The Bandit and Higgins projects are developing open source identity services to help individuals and organizations by providing a consistent approach to managing digital identity information regardless of the underlying technology. This reference application leverages the information card metaphor that allows an individual to use different digital identity ‘I-Cards’ to gain access to online sites and services. This is the metaphor used in the Window’s CardSpace identity management system that ships with the Vista* operating system.
“Windows CardSpace is an implementation of Microsoft’s vision of an identity metasystem, which we have promoted as a model for identity interoperability,†said Kim Cameron, architect for identity and access at Microsoft. “It’s rewarding to see the Bandit and Higgins projects, as well as the larger open source community, embracing this concept and delivering on the promise of identity interoperability.â€
The open source technology developed by Bandit and Higgins enables initial integration between a non-Liberty Alliance identity system and a Liberty Alliance-based federated identity system provided by Novell Access Manager. Specifically, these technologies enable Novell Access Manager to authenticate a user via a Microsoft infocard (CardSpace) and consume identity information from an external identity system. It will further show that identity information from Novell Access Manager can be used within an infocard system. This is a significant step forward in the integration of separate identity systems to deliver a seamless experience for the user as demonstrated by the reference application.
“The Liberty Alliance project fully supports the development of open source identity services that advance the deployment of Liberty-enabled federation and Web Services as part of the broader Internet identity layer,†said Brett McDowell, executive director of the Liberty Alliance. “The open source community’s embrace of Liberty Alliance protocols is validation of the benefits this technology provides, and we salute the Bandit and Higgins teams for their role in making the technology more broadly accessible.â€
Higgins is an open source software project that is developing an extensible, platform-independent, identity protocol-independent software framework to support existing and new applications that give users more convenience, privacy and control over their identity information. The reference application leverages several parts of Higgins including an identity abstraction layer called the Identity Attribute Service (IdAS). To support a dynamic environment where sources of identity information may change, it is necessary to provide a common means to access identity and attribute information from across multiple identity repositories. The IdAS virtualizes identity sources and provides a unified view of identity information. Different identity stores or identity management systems can connect to the IdAS via “context providers†and thus provide interoperability among multiple systems.
“Many groups have been working towards the goals of Internet identity interoperability,†said Paul Trevithick, technology lead for the Higgins project. “This milestone represents a major step in having multiple open source projects work together to support multi-protocol interoperability.â€
The Bandit project, sponsored by Novell, is focused on delivering a consistent approach to enterprise identity management challenges, including secure access and compliance reporting. The Bandit team’s contributions to the reference application include the development of multiple “context providers†that plug into the Higgins Identity Attribute Service (IdAS) abstraction layer to provide access to identity information across disparate identity stores. It also showcases the role engine and audit reporting capabilities in development by the Bandit community.
“The development of this reference application would not have been possible without the collaboration and contribution of the wider Internet identity community,†said Dale Olds, Bandit project lead and distinguished engineer for Novell. “This is the first of many milestones we are working towards as both the Bandit and Higgins communities strive to enable interoperable, open source identity services.â€
So congratulations to Bandit, Higgins and everyone else who made this happen – this is great stuff, and the identity big bang is one step closer for it.
