With the latest CardSpace bits anyone who is handy with HTML and PHP, Ruby, C#, Python or almost any other language can set up CardSpace on their site in minutes – without the pain and expense of installing a certificate. They can do this without using any of the special libraries necessary to support high security Information Card exchanges.
This approach is only advisable for personal sites like blogs – but of course, there are millions of blogs being born every second, or… something like that. Students and others who want to see the basic ideas of the Metasystem can therefore get into the game more easily, and upgrade to certificates once they've mastered the basics.
I've put together a demo of everything it takes to be successful (assuming you have the right software installed, as described later in this piece).
From the high security end of the spectrum to the long tail
Given the time pressures of shipping Vista, those of us working on CardSpace had to prioritize (i.e. cut) our features in order to get everything tested and out the door on schedule. One assumption we decided to make for V1.0 was that every site would have an X.509 certificate. We wanted our design to start from the high end of the security spectrum so the fundamental security architecture would be right. Our thinking was that if we could get these cases working, enabling the “long tail” of sites that don't have certificates would be possible too.
Let's face it. Getting a certificate, setting up a dedicated external IP address, and configuring your web server to use https is non-trivial for the average person. Nor does it make much sense to require certificates for personal web sites with no actual monetary or hacker value. I would even say that without proper security analysis, vetting of software and rigorous operating procedures, SSL isn't even likey to offer much protection against common attacks. We need to evolve our whole digital framework towards better security practices, not just mandate certificates and think we're done.
So again, when all is said and done, it is best to promote an inclusive Identity Metasystem embracing the full range of identity scenarios – including support for the “long tail” of personal and non-commercial sites. One way to do this is through OpenID support. But in addition, we have extended CardSpace to work with sites that don't have a certificate.
The user experience makes the difference clear – we are careful to clearly point out that the exchange of identity is not encrypted.
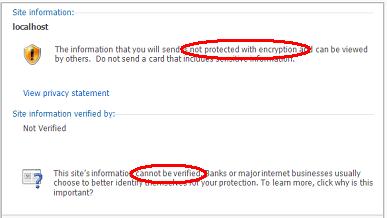
In spite of this, CardSpace continues to provide significant protection against attack when compared with current browsers. You are shown the DNS name of the site you are visiting as part of the CardSpace ceremony, not on some random screen under the control (or manipulation) of a potentially evil party. And if you have been redirected to a “look-alike” site containing an unknown DNS name, you will get the “Introductory” ceremony rather than the more streamlined “Known site” ceremony. This unexpected behavior has been shown to make people much more careful about what is appearing on their screen. Ruchi from the CardSpace blog has a great discussion of all the potential issues here.
What software is required?
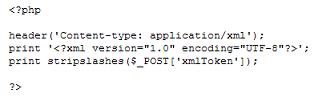
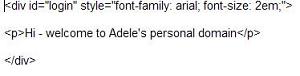
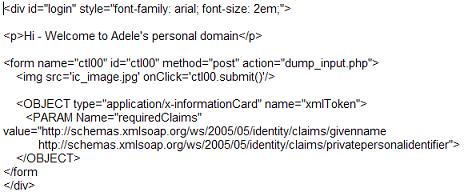
As my little demo shows, if you have a website to which you want to add CardSpace support, all you need to do is add an “object tag” to your login page and parse a bit of xml when you get the Information Card posted back to your site.
On the “client” side, if you are using IE, first you will need to install an updated browser specific extension that will work at a non-SSL site. If you have IE7 you probably already have it as part of the October security update. If not, download it from here.
Second you will need to install an updated version of Cardspace that does the right thing when a website (we call it the “relying party”) does not have a certificate. The latest version of Cardspace can be downloaded as part of .Net Framework 3.5 from here.
For people using Mac and Linux clients, I look forward to the upcoming Internet Identity Workshop as an opportunity to catch up with my friends from Bandit, OpenInfoCard, Higgins and others about open source support for the same functionality. I'll pass on any information I can at that time.
Once you watch the demo, more information is available here and here and here. The code snippets shown are here.






 Identifying yourself online is becoming increasingly difficult and dangerous. Most people who use the web have to maintain several usernames and passwords and have to remember which usernames and passwords to use at the various sites they use.
Identifying yourself online is becoming increasingly difficult and dangerous. Most people who use the web have to maintain several usernames and passwords and have to remember which usernames and passwords to use at the various sites they use.